
In this second article, we are going to cover the File to Tape strategy.
Why tape devices are still widely present in the IT department?
- It’s a good way (but not the only one) to manage the offline backup data (read it as improving the Security Strategy of your data).
- Media can be easily carried or moved (read it as Portability).
- Deployment is often very quickly (read it as speeding up the adoption).
- It has a potentially infinite capacity (Just adding media).
- The LTO is a neverending technology in a continued evolution.
- The tape is a well-known device, IT operators have the skills to manage it.
- The costs for GB is lower than disk technologies.
- The costs are quite predictable, managers can budget it easily.
VBR needs a Windows Physical Server named Tape Server to control the Drives and Robotic, LTO3 or later Drives, and MS-Windows drivers (supply by the hardware vendor).
The official user guide available on the Veeam site gives all detailed info.
Just a note before starting:
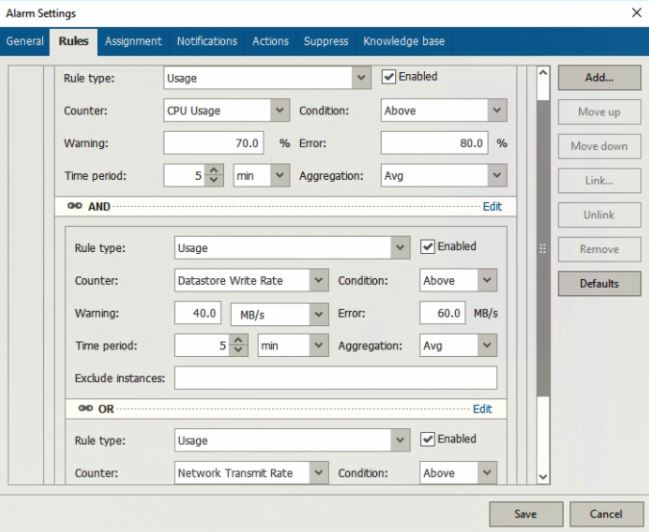
VBR uses Tape Technology in two different ways.
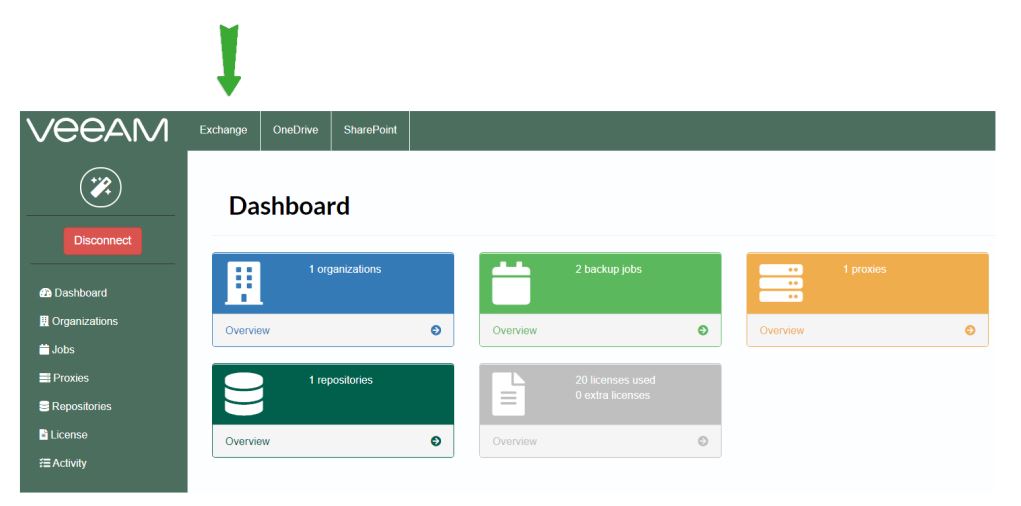
The most used one is back up to tape (Picture 1).
In this case, the source backup data are the backups already present and created with a backup job or backup copy job.
They are saved to Repository (Repository is a Disk technology).
It means that the scope of backup to tape is to pour out data to tape.
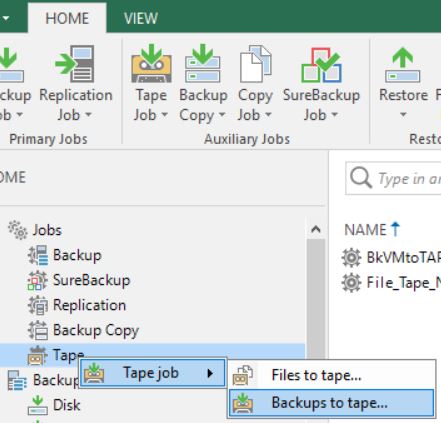 Picture 1
Picture 1
Please have a look at the following video (https://www.youtube.com/watch?v=Il8mH2KB_Uo) to get more details.
The second way is File to Tape and it is the topic of this article (picture 2).
 Picture 2
Picture 2
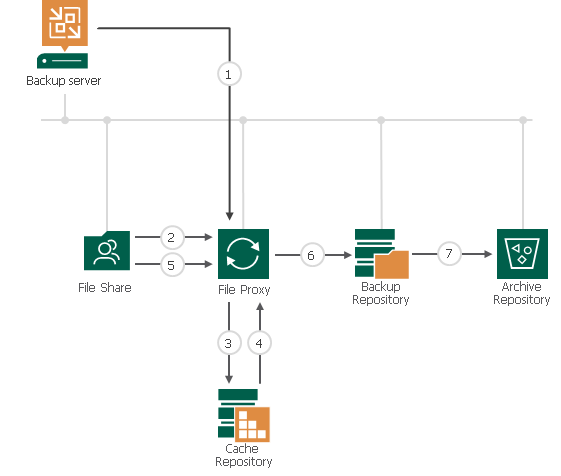
Which type of source files can be saved to tape?
- Windows & Linux servers (virtual or physical doesn’t matter)
- NAS file share (SMB (CIFS) and NFS ).
- NDMP filers (it will be covered in the next article).
- How does it work?
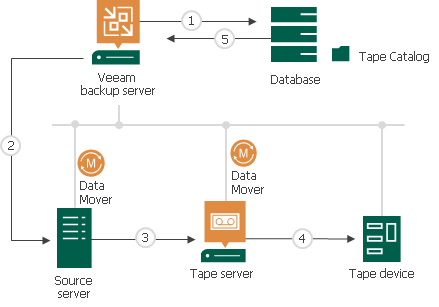 Picture 3
Picture 3
Picture 3 shows the data streams when a tape process is performed:
- The main components are Data Movers. These Services run on the source and on the Tape Server.
- VBR triggers the source Data Mover to perform a copy of the files to the target. At the destination, the target Data Mover check if the files have arrived correctly.
- The tape Server manages the write operation to the tape also.
- VBR stores all info about files saved (media used, retention, etc.) in a catalog.
- In the restore scenario, the step order is four to one.
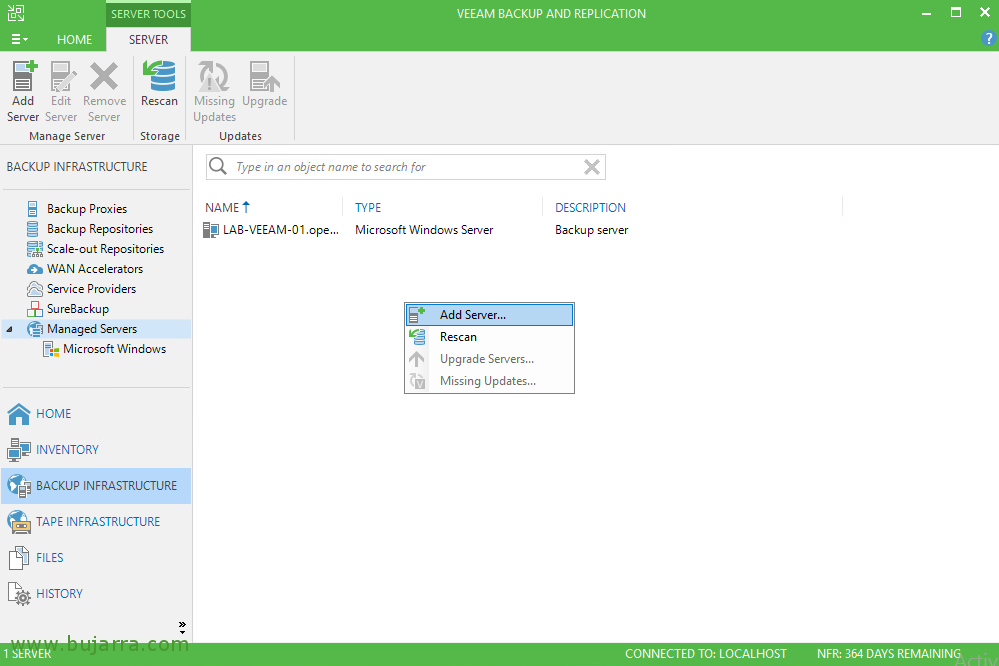
- *Note: To perform a backup of Windows and Linux servers, it is requested to add those servers to the managed server as shown in picture 3. Through this process, the Data mover service is properly installed.
- Network Share: Adding SMB/NFS Share as shown in the previous article (A Flexible file backup strategy – Part 1).
 Picture 3
Picture 3- Common scenarios
File to Tape backup can be used by any customer. You need just a Tape Server, Tape Devices, Drivers, and VBR.
There are at least two main cases:
- Customers who want a copy of their data to tape.
- Customers with a small budget who doesn’t need rapid restore
The next video will show how to set it up.
Main Pro
- There is not a room limit. It means the license doesn’t count how many GB, TB, PB will be written to Tape.
- The VBR architecture is as usual flexible. It’s possible to add more tape servers and more than 1 tape library.
Version 11 will add more great features:
- Tape cloning (https://community.veeam.com/blogs-and-podcasts-57/tape-improvements-in-vbr-v11-277)
- Tape verification (https://community.veeam.com/blogs-and-podcasts-57/part-ii-tape-improvements-in-vbr-v11-289)
Cons
*This behavior is quite common to all backup software that writes data directly to Tape.
- For saving a file, VBR needs to trigger a process of discovering the file to the source, gathering and writing it to a media.
If you consider that the common NAS scenario is composed of millions of small files and thousands of folders and that the tape technology has to choose for every file the location in the media (where the file will be copied) it’s clear that this process, common to all backup servers, stresses the hardware architecture and in particular the drive header.
The backup process has a small speed advantage compared to restoring because writings to media are often sequential and not random.
Image to restore 10k files located in 10k different positions in a single tape.
The drive has to perform a great job. It is going to suffer from an effect called shoe-shining (also known as tape back-hitching) which occurs when a tape drive cannot transfer data at an acceptable speed.
Shoe shining can contribute to data loss over time, as the repeated back-and-forth motion will wear the tape drive’s read/write heads and negatively affect the readable portion of the tape
- Loss of Tape Cartridge Capacity
- Increased Risk of Read/Write Issues
- Excessively Worn Tape Drive Heads
- Low Data Transfer Rates
- Data Loss
- The Veeam DB needs to be sized correctly and the best practice is to switch from SQL Express to SQL Standard
- Media management is quite challenging when the amount of tapes is big. Remember to store them in a fireproof and non-magnetic safe.
Do you also prefer the NAS backup feature introduced in v.10? Let me know!
That’s all for now.
See you next week for talking about NDMP


 Picture 1
Picture 1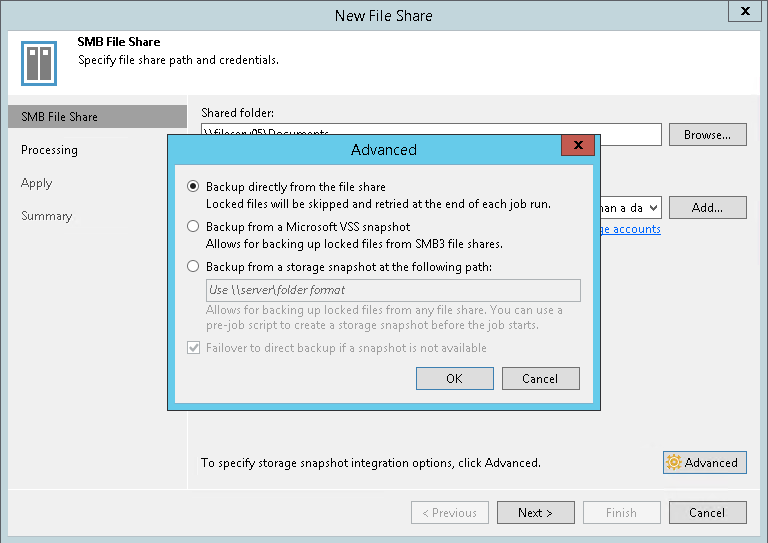 Picture 2
Picture 2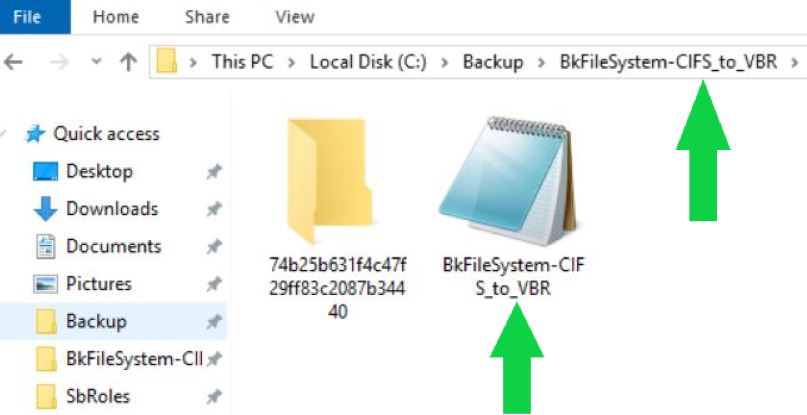 Picture 3
Picture 3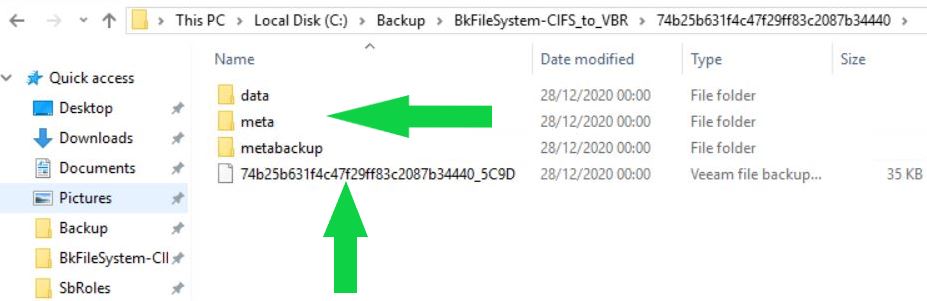 Picture 4
Picture 4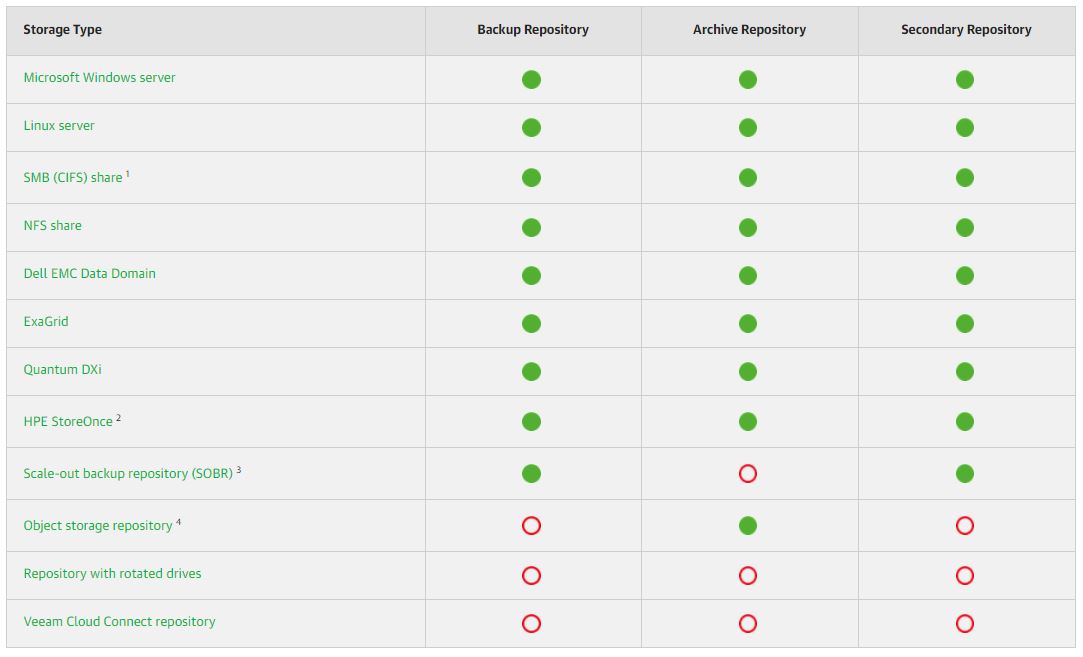 Picture 5
Picture 5

 Picture 1
Picture 1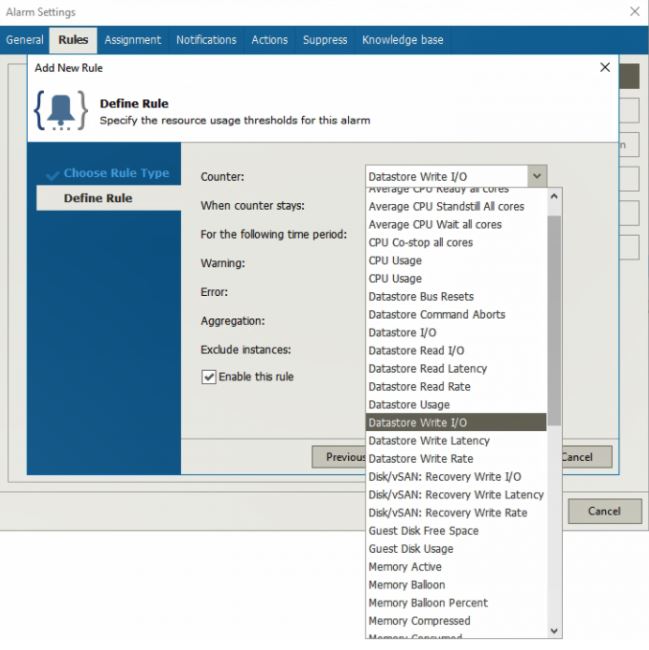 Picture 2
Picture 2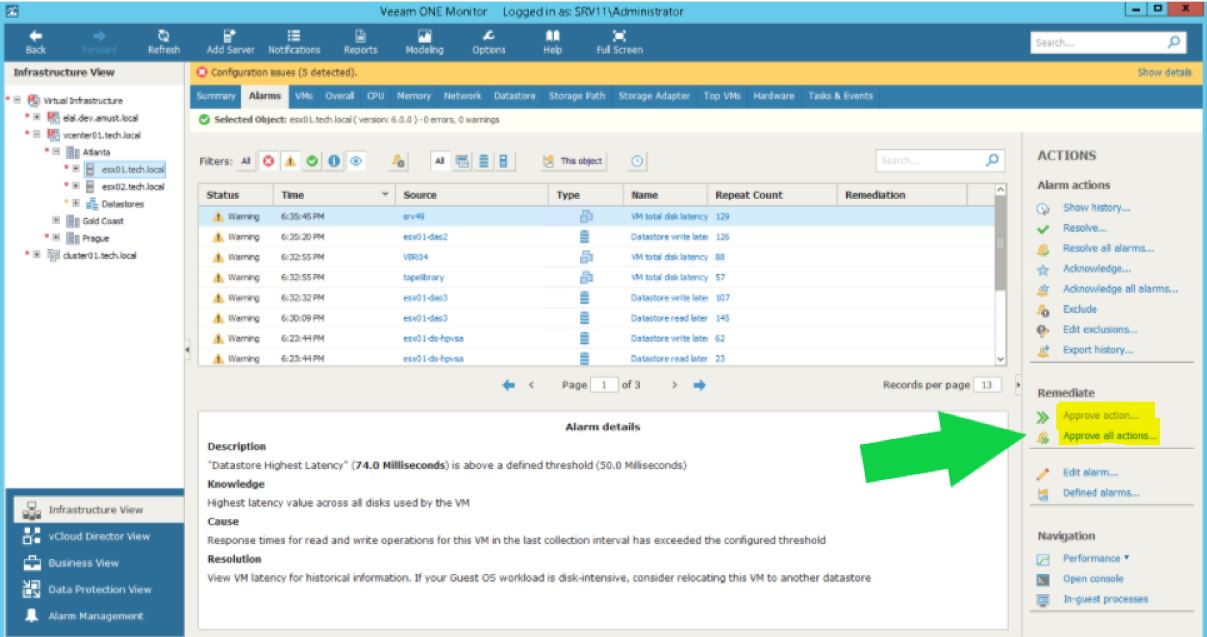 Picture 3
Picture 3
 Picture 1
Picture 1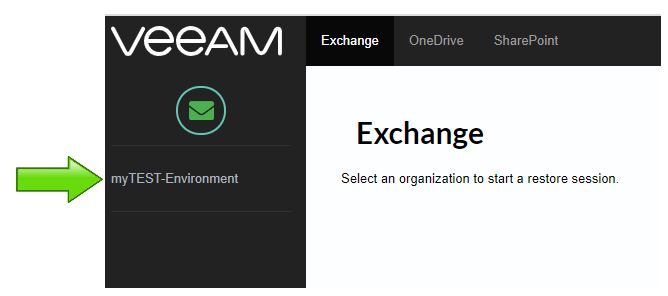 Picture 2
Picture 2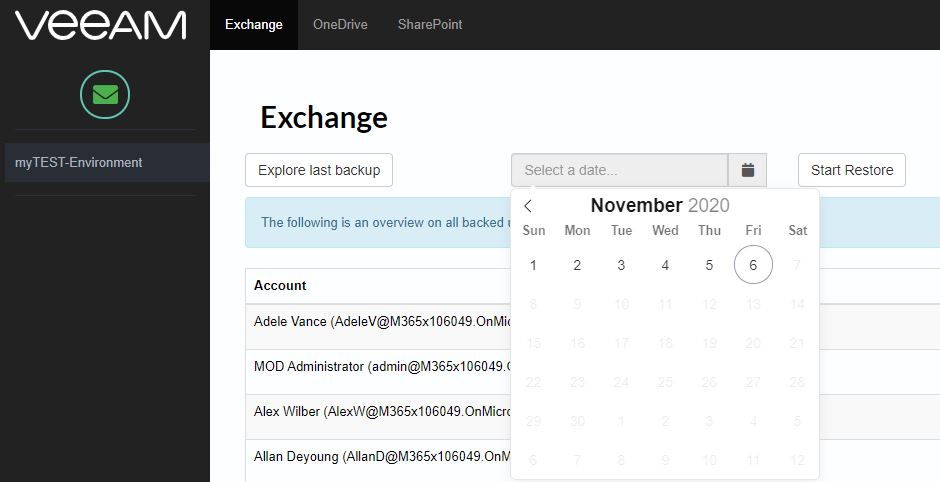 Picture 3
Picture 3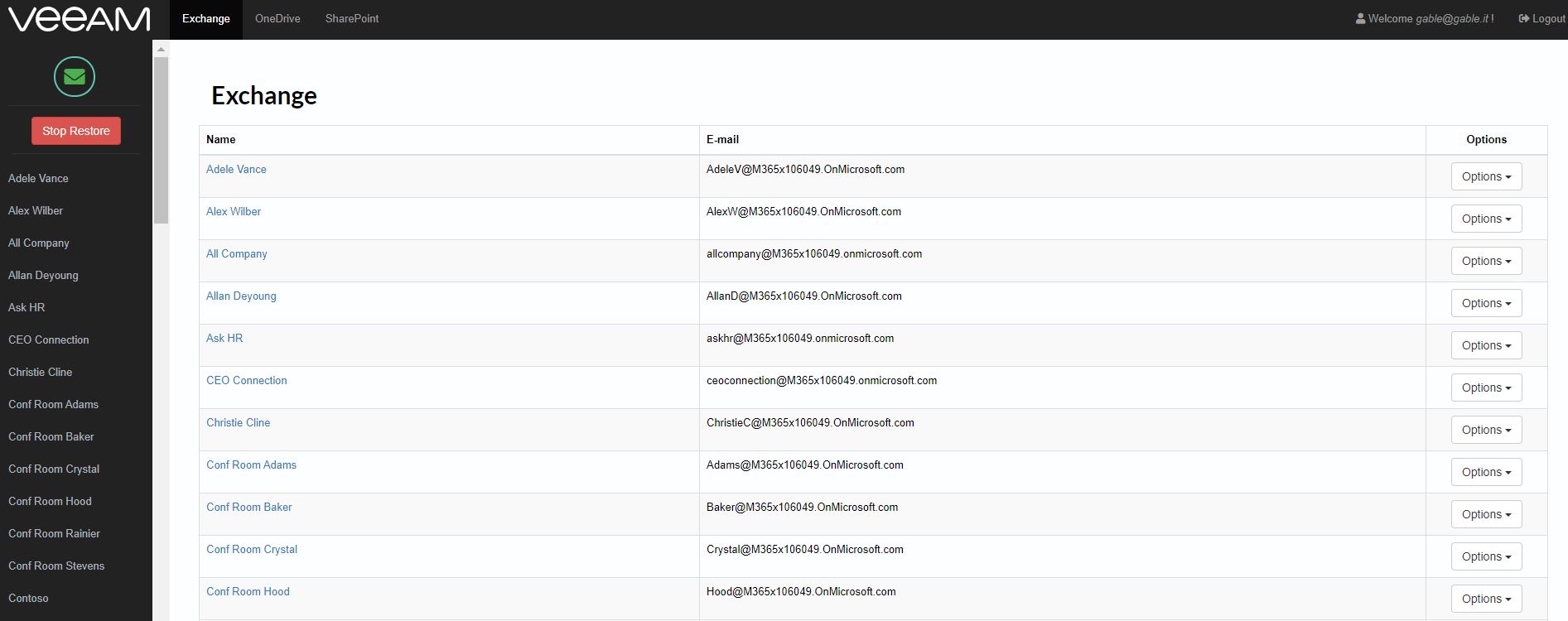 Picture 4
Picture 4 Picture 5
Picture 5 Picture 6
Picture 6 Picture 7
Picture 7 Picture 8
Picture 8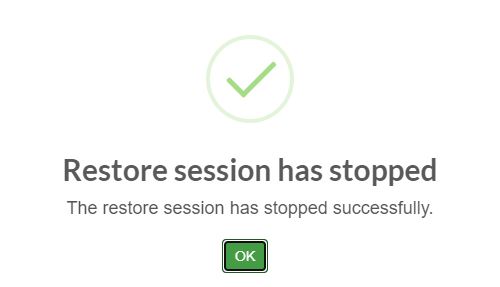 Picture 9
Picture 9 Picture 10
Picture 10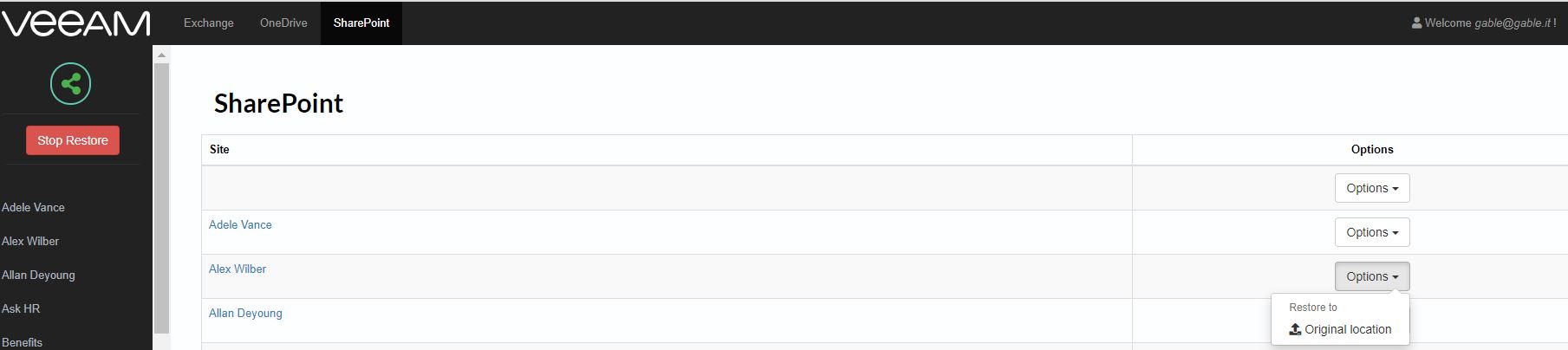 Picture 11
Picture 11